When the Data Stops Being Used: Why Secure Disposal of IT Assets Matters
In today’s digital age organisations generate, process and store vast volumes of data on computers, servers, backup tapes, mobile devices and other IT assets. Much attention is rightly paid to protecting data while it is in use — encryption, access control, network security and so on. But what happens when those assets reach the end of their working life? Too often, the disposal or repurposing of equipment storing data is overlooked. That’s where risk creeps in — and where the expertise of Meerkat Security comes in.
Why end‑of‑life disposal matters
Residual Data Risk
Even when an asset is retired, data may remain on storage media — hard drives, SSDs, tape backups, USBs. Without secure erasure or destruction, that data can be recovered by someone with the right tools. According to guidance from the National Cyber Security Centre (NCSC), secure sanitisation of storage media is critical — including degaussing or physical destruction when reuse is not intended. NCSC+1Regulatory & Legal Obligations
Under the UK GDPR and the Data Protection Act 2018, organisations must ensure that personal data is processed securely, including protection against “unauthorised or unlawful processing and against accidental loss, destruction or damage.” GDPR+1
Disposal therefore isn’t simply a matter of tossing equipment — it must be managed, documented and executed in a way that meets your accountability obligations.Storage Limitation & Retention Policy
One of the key principles of the GDPR is storage limitation — data must not be kept longer than necessary for the purpose it was collected. ICO+1 When IT equipment reaches end‑of‑life, the data on it may no longer be required. Failing to dispose of or anonymise that data exposes you to unnecessary risk, cost and potential regulatory action.Reputation, Cost & Environmental Impact
A data breach from discarded equipment can cause reputational damage, regulatory fines and customer trust loss. Secure disposal also offers an opportunity to repurpose or recycle equipment responsibly — reducing environmental impact and supporting sustainable business practices.

What secure disposal looks like
At Meerkat Security we recommend a structured end‑of‑life asset disposal process including:
Inventory & Tracking: Maintain a register of assets that reach end of life, including device type, serial numbers, storage media, last known data type.
Data Classification & Erasure Plan: Determine what data remains on the device, assess sensitivity, decide whether secure wiping (if reuse) or destruction (if disposal) is required.
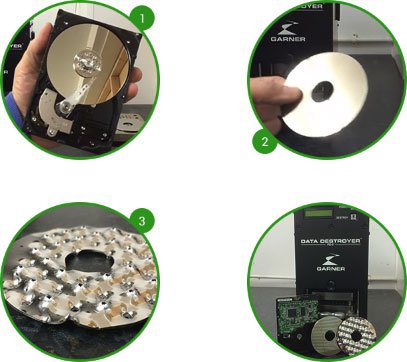
Certified Methods: Use recognised methods such as secure software wiping (multiple passes or certified standard), degaussing (for magnetic media) or physical destruction/shredding/crushing of drives. Varese Secure+1
Chain‑of‑Custody & Documentation: Maintain proof that the asset was disposed of securely — e.g., chain‑of‑custody logs, certificate of destruction, audit‑trail. The Information Commissioner’s Office (ICO) recommends documenting methods used and storing logs of devices sent for disposal. ICO+1
Reuse/Repurpose or Recycling: If assets are to be reused internally or sold/given to others, ensure data is fully wiped and reuse is secure. If equipment is to be recycled, ensure any storage media is destroyed or rendered unrecoverable first.
Policy & Awareness: Embed asset disposal into your overall data governance, include it in your data retention & destruction policy, train staff on responsibilities. Restore
Why choose Meerkat Security for secure disposal
We understand the full lifecycle of data and IT assets — from creation, protection, through to secure end‑of‑life.
We deliver on disposal services including certified secure erasure, on‑site or off‑site destruction, audit trails and certificates for assurance.
We integrate with your existing environment (e.g., your active directory, SCCM, Meraki network, Intune endpoint estate) to identify assets, map risk and verify disposal.
Our approach addresses both regulatory compliance (UK GDPR, ICO guidance) and business risk (reputation, cost, sustainability).

If your organisation has unused, end‑of‑life IT equipment (computers, servers, storage arrays, backup tapes or mobile devices),and you want to ensure that data on them won’t become a future liability, contact Meerkat Security today. Let’s ensure your data is protected not just whilst it’s in use, but also when it’s time to securely say goodbye.